Recently, another novelty in the malware arena has been released. The LOBSHOT is a new malware family that has been causing a stir in the cybersecurity world lately. This potent tool combines backdoor and spyware functionality, making it malware to be reckoned with. Moreover, LOBSHOT uses clever and unusual tactics to spread itself around, making it even more effective. A significant aspect of it is its capability to generate. Hidden VNC connections may be of interest to many cybercriminals. So, how dangerous is LOBSHOT really? This article will explore what it is, how it spreads, and how to protect your crypto wallets against it.
What is LOBSHOT malware?
In mid-2022, a new type of malware known as LOBSHOT surfaced, exhibiting advanced stealer capabilities and backdoor functionality. However, despite its capabilities, its primary purpose is stealing cryptocurrency wallets, particularly crypto browser extensions. As a result, its narrow specialization makes it more discreet. Furthermore, LOBSHOT’s use of hVNC is rather unusual. Not surprisingly, this malware is attributed to the russian cybercrime gang TA505, best known for their Cl0p ransomware. This thesis appeared due to LOBSHOT’s use of the group’s infrastructure as C2 servers for this malware. Although the gang typically focuses on corporations and governments, LOBSHOT is aimed at individual users.
Spread methods
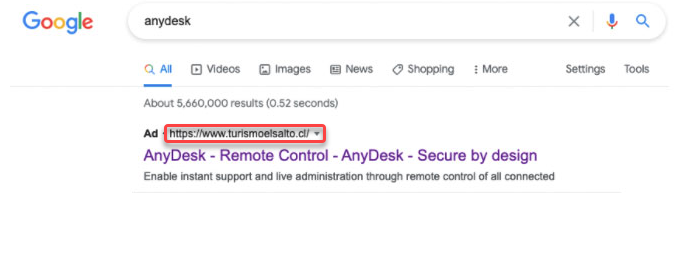
Although phishing is the primary and most popular method of spreading any malware of this kind, recently, there has been an increase in cyber threats through Google Ads. Thus individuals have unknowingly been exposed to LOBSHOT malware that falsely plays legitimate software. For example, there can be free apps for remote workers like AnyDesk.
Malicious advertisements in Google Ads
The malware generally bears on malicious advertisements in Google Ads – a pretty rare approach. It supposes creating a landing site that resembles a downloading page of a well-known free software vendor. Then, crooks purchase a promotion from Google, posting it to search results. Because of plentiful SEO spam used on that counterfeit, it is getting boosted to the top of search results – GridinSoft Research team.
This is similar to a tactic observed earlier this year with Rhadamanthys Stealer. Then malware was spread through Google Ads, posing as download sites for popular remote-workforce software like AnyDesk and Zoom. Investigators have noted a significant rise in malvertising since the beginning of the year, and many users were falling victims to fake ads. Security experts warn that this trend of using malvertising to spread malware will continue as cyber adversaries become more persistent in impersonating legitimate software.
Stealer functionality
As previously mentioned, LOBSHOT targets cryptocurrency wallets. It focuses on browser extensions and scanning for Firefox, Edge, and Chrome extensions. It checks for extensions by their IDs and files. When it finds a matching extension, it alters the DefaultPrinter value by adding a string that represents the extension in the format “Browsername_Extension”. For example, if it finds the Yoroi plugin in Chrome, it adds the line “Chrome_Yoroi” to the value. The following extensions may be of interest to LOBSHOT:
Chrome
- TronLink
- XDEFI Wallet
- Binance Wallet
- MetaMask
- BitApp
- Guarda
- MyEtherWallet
- iWallet
- EVER
- KardiaChain Wallet
- Brave Wallet
- Nifty Wallet
- Jaxx Liberty
- GuildWallet
- Station
- Oxygen
- Phantom
- Pali Wallet
- Math Wallet
- Ronin Wallet
- Yoroi
- MultiversX DeFi Wallet
- Liquality Wallet
- Wombat, Coin98
- Harmony
- Saturn Wallet
- Equal, Nami
- BOLT X
Firefox
- TronLink
- Ronin Wallet
- Phantom
- MetaMask
- Yoroi
Edge
- Glow
- Ronin Wallet
- BDLT Wallet
- OneKey
- Math Wallet
- Yoroi
- MetaMask
- MetaWallet
- Station Wallet
hVNC feature
One of the key features of LOBSHOT stealer is its ability to create a Hidden Virtual Network Computing connection. This is achieved by creating a hidden desktop through specific system calls without the user of the infected PC being aware of it. The malware then assigns this desktop to itself and adds a new instance of explorer.exe for the hidden desktop. This allows the malware to stream the screen of the hidden desktop to a command server, giving the client hackers control over the infected computer. Additionally, hackers can perform manual actions and use hotkeys to make specific actions easier.
How to protect against LOBSHOT?
Since LOBSHOT has no security evasion features except for Microsoft, we recommended using a third-party anti-malware solution. It’s important to note that LOBSHOT’s developers rely on malicious pages in Google Ads. Therefore having a network monitor is beneficial and helps to solve this issue. Additionally, if LOBSHOT manages to infiltrate your system unnoticed, you should prevent it from running. This, however, requires an advanced anti-malware program. Loaris Trojan Remover is an optimal option due to its detection systems, which can detect known and new malware samples in the modern threat landscape.
